Computer Virus Attack
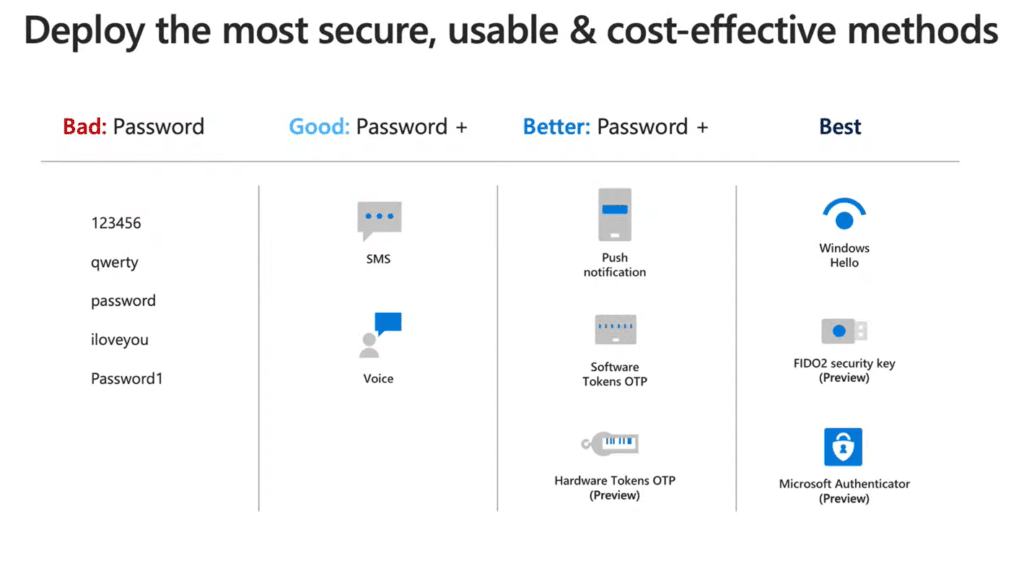
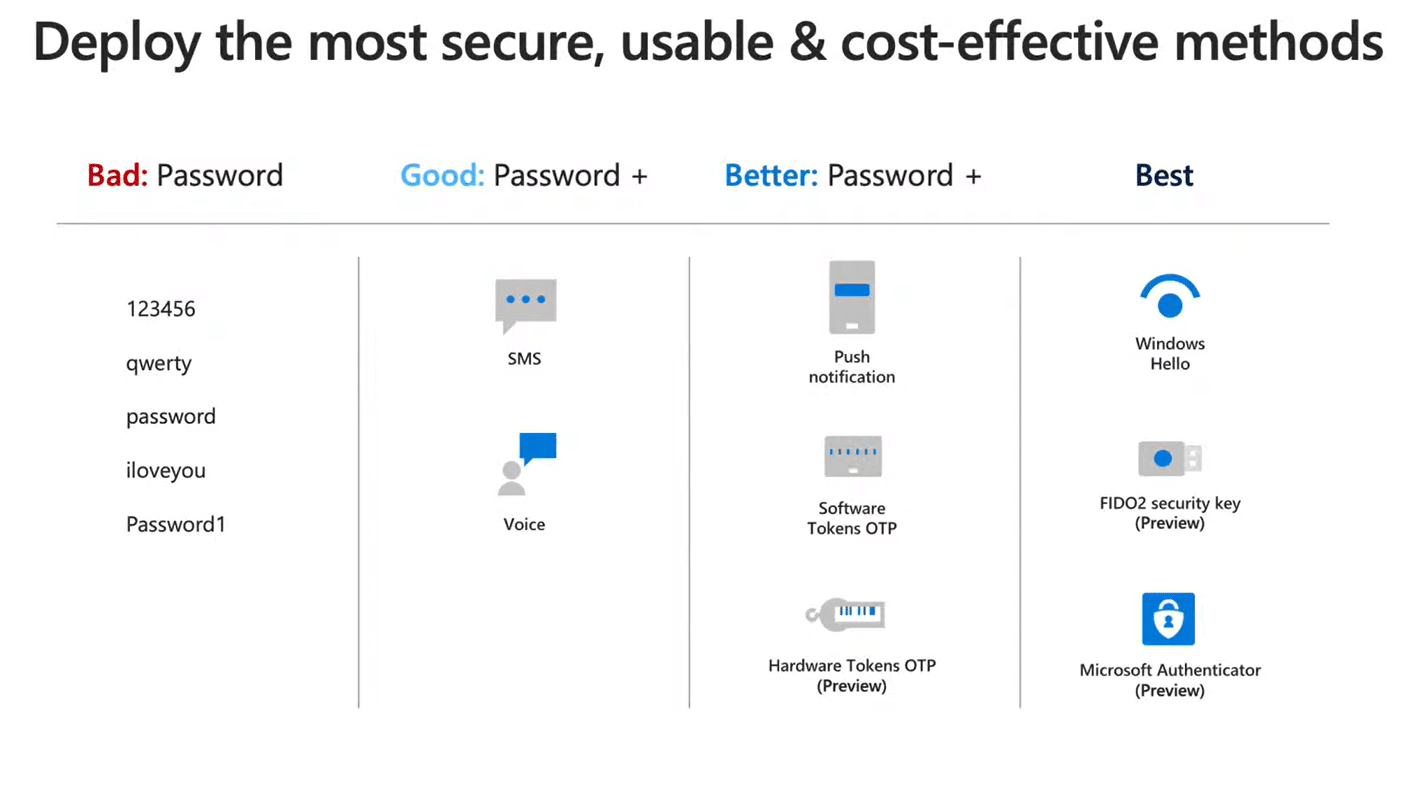
Recomended Password Methods
Recommended Password Methods are FIDO2 Keys, Windows Hello, and Microsoft Authenticator
If you have trouble remembering multiple passwords, use a password manager to automatically update stored passwords, keep them encrypted, and require multi-factor authentication for access. However, deploying a different password method may be your company's best solution. Call Easy IT Support, and we will provide security recommendations for your end users and Cloud applications.
See the video from Microsoft Tech Community