Cyber Security
Recomended Password Methods
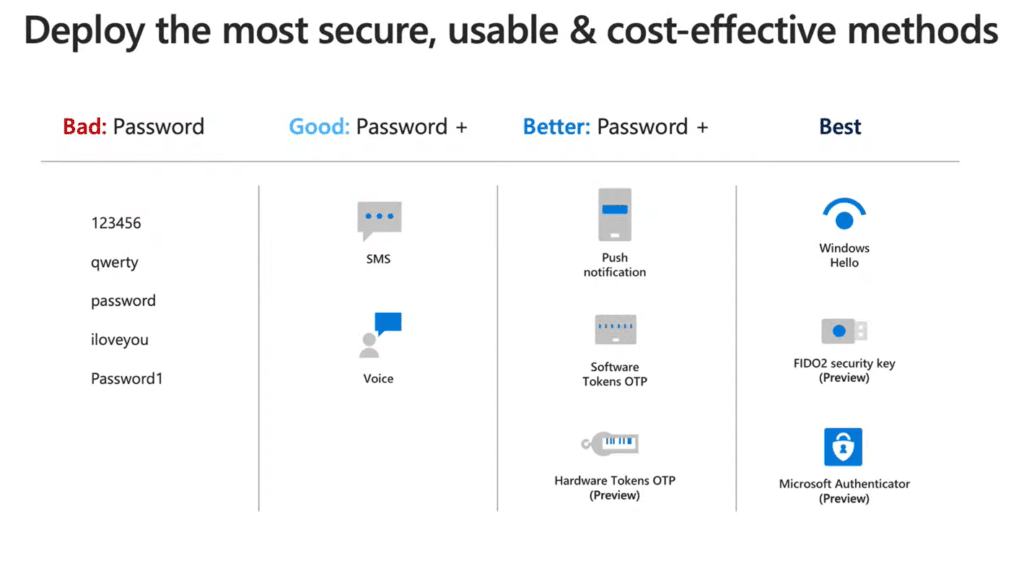
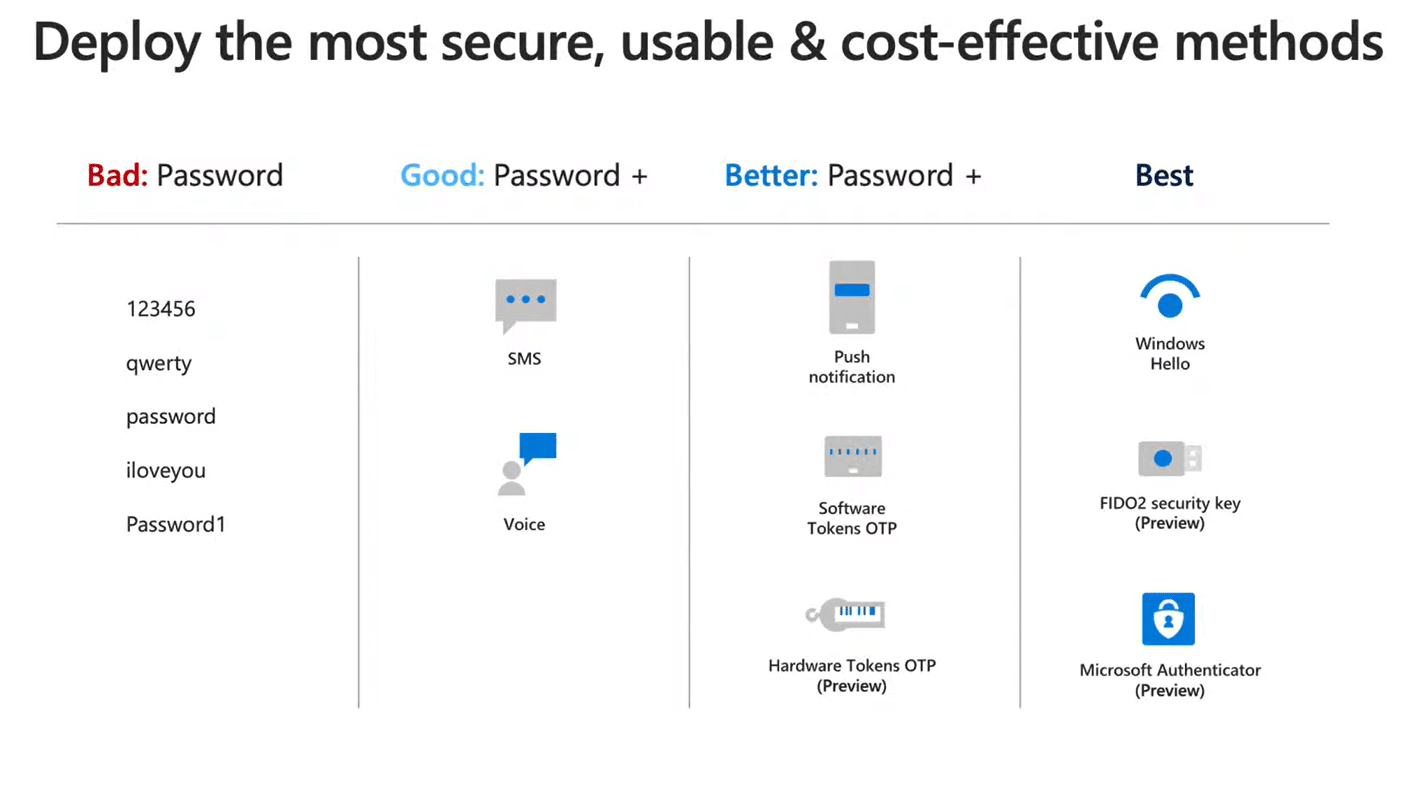
Recommended Password Methods are FIDO2 Keys, Windows Hello, and Microsoft Authenticator
If you have trouble remembering multiple passwords, use a password manager to automatically update stored passwords, keep them encrypted, and require multi-factor authentication for access. However, deploying a different password method may be your company's best solution. Call Easy IT Support, and we will provide security recommendations for your end users and Cloud applications.
See the video from Microsoft Tech Community
Microsoft Sentinel

Partnership with Symantec

Why did Easy IT Support partner with Symantec? Because Symantec is a enterprise grade security for the masses. Cyber safety for consumers!
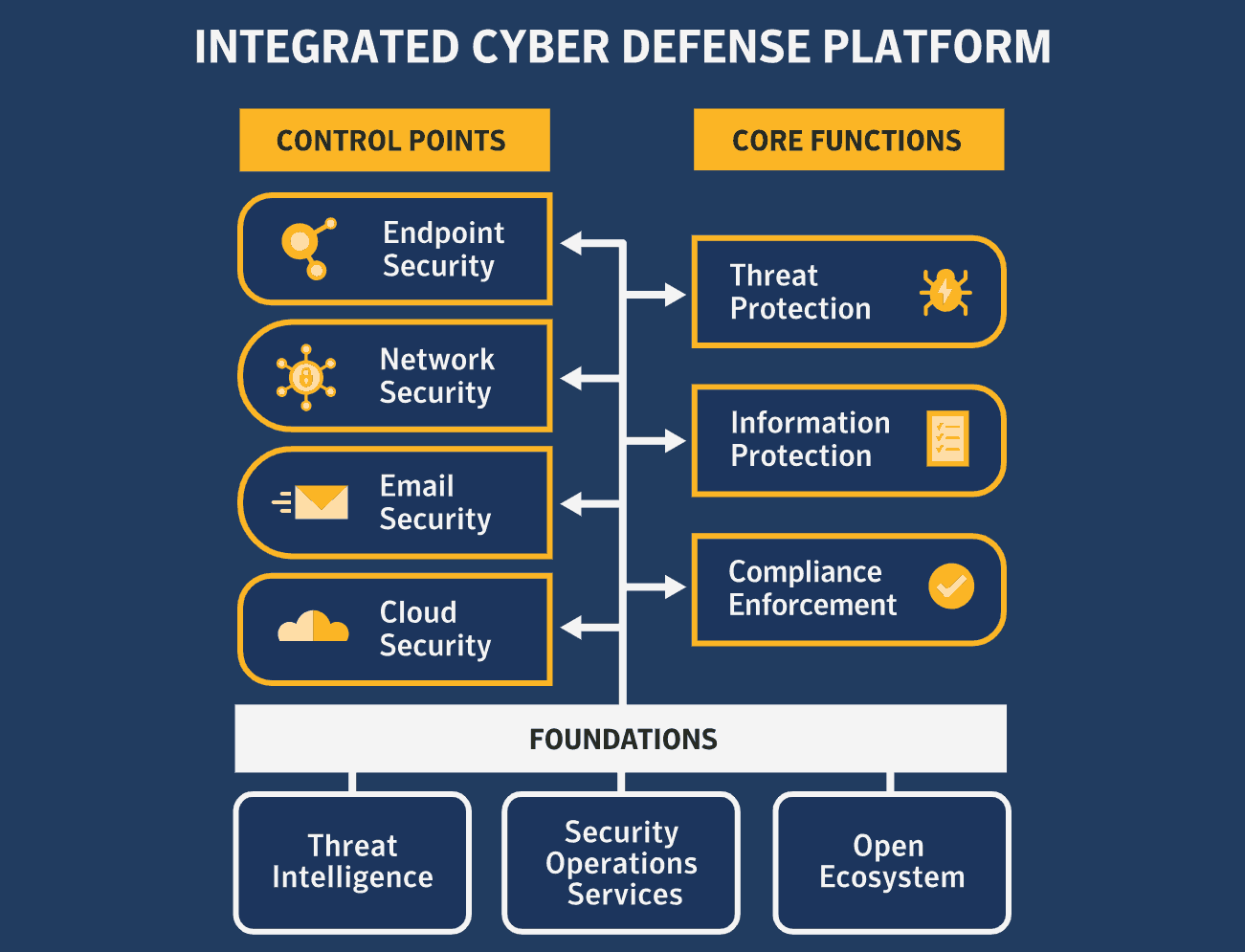
A patchwork of stand-alone security products from multiple vendors is simply too expensive, too complex, and, even worse, it’s proven to be ineffective.
As the world’s leading cyber security company, we deliver a better way forward:
it’s called Integrated Cyber Defense.
An open platform that seamlessly combines security solutions from Symantec and our technology partners into a single framework across devices, networks, cloud, and datacenter infrastructure.
Offering unparalleled
- Threat Prevention
- Detection
- Incident Response
- Managed Security Services
Integrated to reduce complexity for ease of use and lower costs.